Managed IT Services & Support
Computer Hardware Supply

Access Control Systems

Data Recovery and Backup Plan

Network Design
Cloud Services
Cyber Security
We Create Fully Connected Systems So You Can Focus On Your Business
Wanishi will help your organization align its IT infrastructure with its overall business objectives. This includes developing long-term IT strategies that improve business efficiency, scalability, and competitiveness.
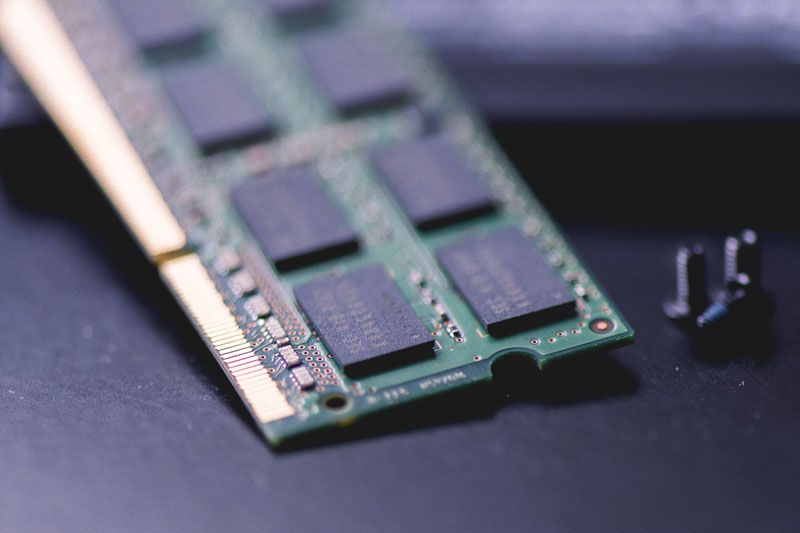
Computer Hardware Supply
At Wanishi, we specialize in providing top-tier computer hardware solutions for businesses, gamers, and tech enthusiasts. Whether you’re building a custom PC, upgrading existing systems, or outfitting your office with the latest tech, we offer a wide range of products designed for performance, durability, and innovation.
Proin Eget Tortor
Pellentesque in Ipsum

Cyber Security Services
Cybersecurity isn’t just about software and firewalls—your hardware is also a critical component in defending against threats like malware, ransomware, and data breaches. Weak points in hardware can provide cybercriminals with unauthorized access to sensitive information. Our range of secure hardware products ensures you stay one step ahead of cyber threats.
Cloud Security
As businesses increasingly use cloud services, securing cloud environments becomes essential to protect data and applications hosted remotely.
Network Security
Network security focuses on protecting a computer network from malicious threats or unauthorized access.
Application Security
Application security focuses on protecting software applications from threats and vulnerabilities throughout their lifecycle, from development to deployment.
Network & Connectivity
Network security focuses on protecting a computer network from malicious threats or unauthorized access.
Firewall
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewalls are designed to protect computer networks from unauthorized access or cyberattacks. They can be implemented in both hardware and software forms, and they typically filter traffic between trusted internal networks and untrusted external networks
Network Access Control
NAC refers to a security solution that manages and controls devices’ access to a network. It is designed to enforce policies regarding which devices can connect to a network and what kind of access they are granted once connected. NAC ensures that only compliant, secure devices can access network resources, helping to prevent unauthorized access and mitigate security risks.
Data Loss Prevention
DLP (Data Loss Prevention) is a set of technologies, strategies, and processes designed to protect sensitive data from unauthorized access, leakage, or loss. The primary goal of DLP is to prevent data breaches, unauthorized sharing, or accidental exposure of sensitive information, such as intellectual property, financial records, personal identifiable information (PII), or health-related data.

We're Here To Help!
Kenya Office
Mayfair Suites 2nd Floor
Parklands Road
P.O BOX 8862-00100
Nairobi-Kenya.
South Africa Office
P.O BOX 4367
Rivonia, South Africa 2128
Call Us
+254715391315
